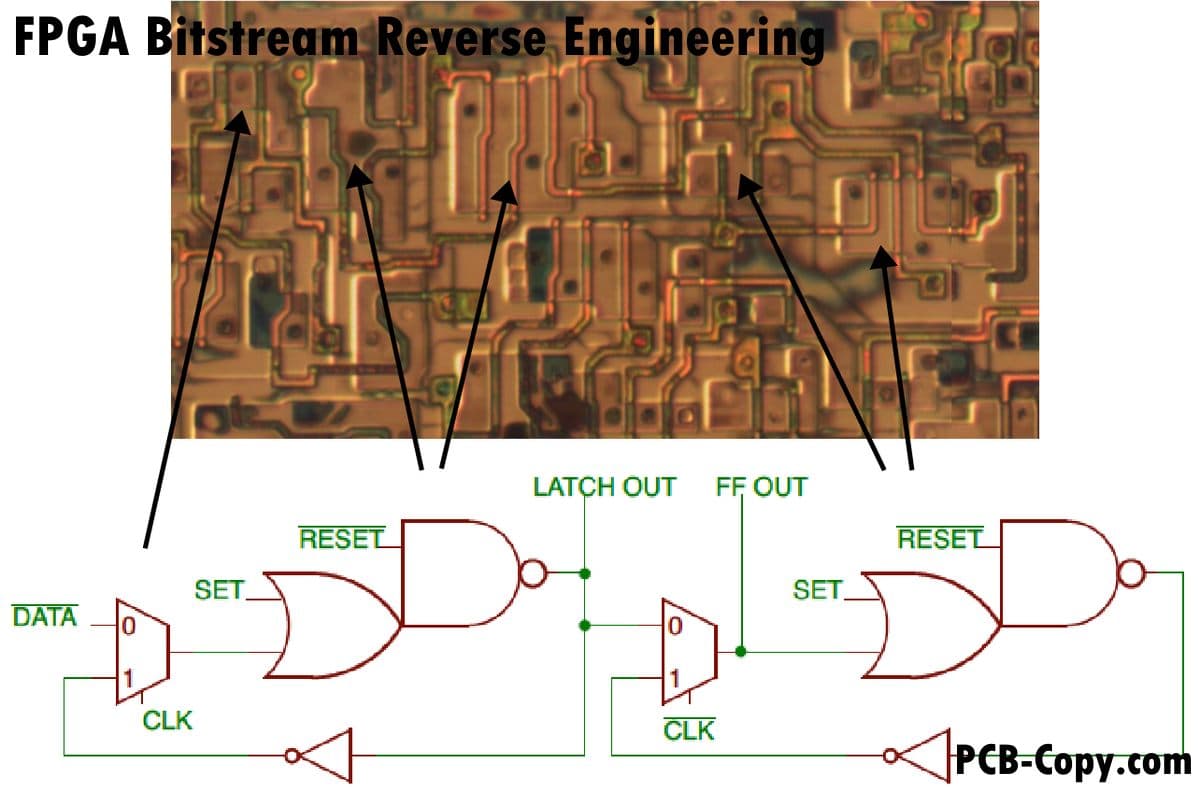
The Technique: Systematic Hardware Documentation
A developer successfully reverse-engineered the proprietary bitstream format of an Altera Cyclone IV FPGA (EP4CE6F17C8) using Claude Code as their primary analysis tool. This wasn't just about understanding the chip—it was about creating a reproducible methodology for hardware documentation that other developers can adapt.
The project's goal was clear: map how each bit in the .rbf (Raw Binary File) configuration controls the FPGA's 6,272 logic elements, 392 LABs (Logic Array Blocks), and routing resources. Commercial FPGA vendors keep these formats closed, forcing developers to use proprietary tools like Quartus. Breaking this dependency requires understanding the chip at the bit level.
Why It Works: Claude Code's Analysis Strengths
Claude Code excels at this type of work because:
- Pattern recognition across large datasets: The developer generated thousands of bitstream variations and used Claude to identify correlations between configuration changes and bitstream differences
- Code generation for automation: All fuzzing scripts were written in Python with Claude's assistance, systematically testing different FPGA configurations
- Documentation synthesis: Claude helped structure findings into coherent documentation about LAB coordinates (X=3,4,6,7... Y=2,3,4...), memory block locations (M9K RAM at X=5,9,20,27), and DSP multiplier positions
- SQLite integration: Experiment results were stored in SQLite databases that Claude could query and analyze
The key insight: Claude Code doesn't just write code—it helps you design experiments, analyze results, and document complex systems.
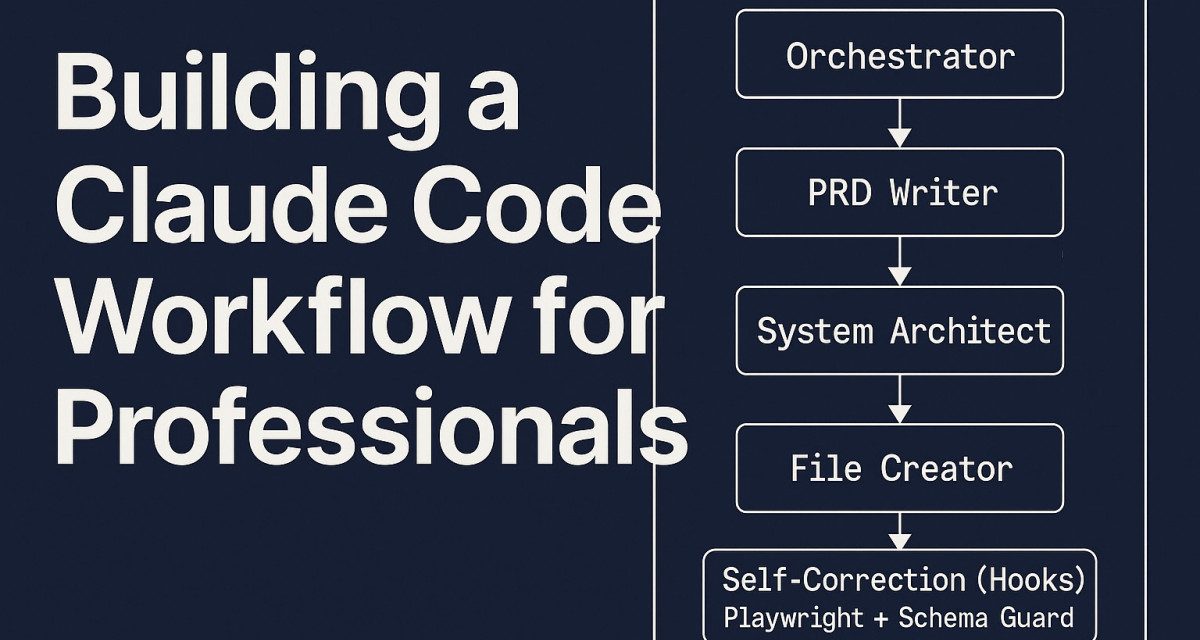
How To Apply This Workflow
Step 1: Set Up Your Toolchain
# Install required tools (adapt paths as needed)
export QUARTUS_PATH="~/intelFPGA_lite/21.1/quartus/bin/"
export OPENFPGALOADER_PATH="$HOME/tools/openFPGALoader/build/openFPGALoader"
# Create your CLAUDE.md with hardware specifics
cat > CLAUDE.md << 'EOF'
Project: FPGA Bitstream Reverse Engineering
Target: Altera Cyclone IV EP4CE6F17C8
Board: Heijin AX301
Tools:
- Quartus Prime 21.1 Lite (synthesis, P&R)
- openFPGALoader (flashing)
- Python 3 + SQLite (analysis)
Chip Layout:
- 392 LABs, 16 LEs each
- LAB X coordinates: [3,4,6,7,8,10,11,12,13,16,17,18,19,21,22,23,24,25,26,28,29,31]
- LAB Y coordinates: [2,3,4,5,6,7,8,9,10,11,12,13,14,16,17,18,19,21]
- Special blocks at X=5,9,14,15,20,27,30 (M9K RAM, DSP, PLL)
EOF
Step 2: Generate Test Bitstreams
Create a Python script with Claude's help to systematically vary FPGA configurations:
# fuzz_config.py - Template for generating test cases
import subprocess
import sqlite3
from pathlib import Path
def generate_bitstream(config_params):
"""Use Quartus tools to generate .rbf from Verilog"""
# Claude can help you write the Quartus TCL commands
# and parameter substitution logic
pass
def analyze_bitstream_difference(base, variant):
"""Compare two bitstreams and log differences"""
# Claude can implement binary diff analysis
# and correlate changes with config parameters
pass
Step 3: Analyze with Claude Code
Use prompts like:
I have 500 bitstream pairs in SQLite table 'experiments'.
Each row has: config_json, bitstream_binary, observed_behavior.
Help me write a query to:
1. Find bits that always change when I enable a specific LAB
2. Map those bits to physical coordinates (X=3-31, Y=2-21)
3. Generate a visualization script of the bitstream layout
Step 4: Document the Format
Claude excels at turning raw data into structured documentation:
Based on these analysis results:
- Bits 0x100-0x120 control LAB at X=6,Y=2
- Bits 0x200-0x220 control routing to adjacent LAB
- Pattern: Each LAB uses 32 control bits
Write a formal specification document with:
1. Bitfield definitions
2. Coordinate mapping tables
3. Example configurations
4. Validation test cases
The Payoff: Open-Source FPGA Toolchains
Once reverse-engineered, this bitstream format enables:
- Open-source toolchains: Use Yosys for synthesis and custom place-and-route tools
- Direct manipulation: Programmatically modify bitstreams for optimization or experimentation
- Educational value: Understand FPGA internals without vendor black boxes
- Portability: Run toolchains on any OS, not just those supported by Quartus
The methodology—systematic variation, automated analysis, and Claude-assisted documentation—applies to any proprietary hardware format you need to understand.
Your Next Hardware Project
Whether you're working with FPGAs, microcontrollers, or custom ASICs, this workflow gives you a template:
- Define your unknown format (bitstream, firmware, configuration ROM)
- Create a test harness with Claude's coding help
- Systematically vary inputs and capture outputs
- Use Claude to find patterns in the resulting data
- Document the reverse-engineered format with examples
The Cyclone IV project proves Claude Code isn't just for software—it's a powerful partner for hardware reverse engineering and documentation.